Role based access control is the permissions model used in Microsoft Exchange 2013. Probably many of you are used to apply RBAC on your Exchange on-premises, based on custom scopes.
In Office 365 there are some limitations when applying scopes to RBAC, such as the Organizational Unit scope. On this post we are going to create a Management Scope based on the custom recipient write scope, and create a Role Group that uses that management scope. What is the main goal? Well in this scenario the main goal is:
Give permissions to specific Help Desk administrators to manage only recipients that have the Department mailbox attribute set to “IT Department”. The administrators added to that role group should not be able to manage any other users.
Note: RBAC customization is not available on all Office 365 plans. To make sure that your plan has RBAC customization see the Exchange Online Service Description.
So let’s get started. The first thing I did was to create 4 users on my Office 365 environment, named User1, User2, User3 and User4. Those 4 users work on the IT department. I also created a user called HelpDeskUser. I want Helpdesk user to be able to manage only the users on the IT Department, in this case User1, User2, User3 and User4. The HelpDesk user is not a member of any other Role Group.
All the users have a license assigned and a mailbox on Office 365.
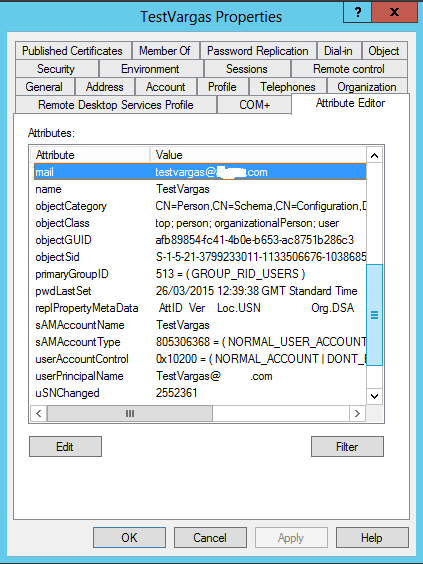
After the user creation I needed to populate the Department attribute on User1 to User4 mailboxes, because that’s the attribute i am going to use on the custom recipient write scope. You can do this in two ways, via the Office 365 Admin Portal or via the Windows Azure Active Directory Module for Windows Powershell.
To do it via the portal, you need to click on “Users > Active Users”, select all the users you want to add the attribute to (you can filter before selecting), and click on “Edit”.

On the Details page populate the Department attribute, as shown above, and click “Next”. If there’s nothing else you want to change, click “Next” on the other pages and click “Submit” on the last one.
To do it via the Windows Azure Active Directory Module for Windows Powershell, start by connecting into the Azure AD as an Administrator (Connect to Azure AD). Once connected, run the following cmdlet to filter the users you want to change the department attribute:
Get-MsolUser -All |where-object {$_.Userprincipalname -like “User*”}
In the cmdlet above I’ve filtered all users with a Userprincipalname that starts with User. You need to adjust the filtering to your specific case.
Once the filtering is returning the expected users, run the following cmdlet to set the department attribute on those users:
Get-MsolUser -All |where-object {$_.Userprincipalname -like “User*”} |Set-MsolUser -Department “IT Department”
To check if the cmdlet applied the attributes successfully run:
Get-MsolUser -All |where-object {$_.Userprincipalname -like “User*”} |fl Userprincipalname, Department

Above you can see the output of all the cmdlets.
Note: In my environment I did the changes on cloud users, as i am not using Dirsync. If you are using Dirsync, and if the users you are changing are synced users, you should make the changes on-premises and force Dirsync (or wait for it to run) to push the attributes to Office 365. Then you can run the last cmdlet shown above to check if the attributes were replicated to Office 365
Once the attribute is defined on all users, we can start configuring RBAC on Exchange Online.
The RBAC configuration is done in two steps:
- Create a Management Scope
- Create a Role Group
To create both you need to open a powershell and connect it to Exchange Online.
Once you are connected to Exchange Online you can start configuring RBAC. I started by running the following cmdlets, to list all my current Role Groups and Management Scopes:
Get-RoleGroup
Get-ManagementScope
 As you can see above, I only have the custom role groups and i have no Management Scopes created.
As you can see above, I only have the custom role groups and i have no Management Scopes created.
So now let’s create the Management Scope. The scope will have a recipient filter, and one of the questions that I get a lot is, “How do we know if this filter is accurate?”. Well the answer is simple: Test the filter before creating the scope, by using the “Get-Recipient -Filter” cmdlet. To test my filter i ran the following:
Get-Recipient -Filter {Department -eq “IT Department”}

My filter is returning the exact users I want to apply the scope to, so i can now create the Management Scope, by running the following:
New-ManagementScope “HelpDesk for IT Users” -RecipientRestrictionFilter {Department -eq “IT Department”}
With the command above i created a management scope named “HepDesk for IT Users” with a recipient restriction filter for all users with the “IT Department” value on the “Department” attribute.
Note: To create a new management scope you might need to run the Enable-OrganizationCustomization cmdlet first. If you don’t you might get an error, as shown below.

Once the management scope is created we can create the Role Group. Just as when you created the management scope, to create the role group you also need to be connected to the Exchange Online powershell, and run the following cmdlet:
New-RoleGroup -Name “HelpDesk IT Department” -Roles “Mail Recipients”, “Reset Password”, “Distribution Groups”, “Mail Recipient Creation” -Members “HelpDeskUser” -CustomRecipientWriteScope “HelpDesk for IT Users” -ManagedBy “Organization Management”

The command above will create a role group named “HelpDesk IT Department”, with 4 roles that will allow it’s members to manage mailboxes and distribution groups, add the “HelpDeskUser” as a member of the group, assign the previously created management scope to the group, and make it managed by the members of the “Organization Management” role group. For more information on which roles you should assign to your role group, click here.
On the Exchange Online Admin Center you can see the new role group, and if you select it, on the right pane you can see the roles, members and write scope assigned to it.

So once that is done… it’s job done!!! 🙂
But, lets do some testing, shall we?
Start by logging into Office 365 with the admin account added to the group, by going to https://outlook.office365.com/ecp/
Try and edit the Organization properties of a mailbox outside of the scope. You should see that the properties are grayed out, which means that the settings applied correctly and you can’t change it.

Now let’s try and edit the Organization properties of a mailbox from the IT Department. You should see the properties available for editing.

So the Role Group is configured correctly.
Job done.. and tested!